
Moonlock, a leading cybersecurity firm, has issued an urgent warning to the crypto community after uncovering a sharp rise in hacks involving a fraudulent version of the Ledger Live application.
Originally designed to manage Ledger cold wallets, Ledger Live has become the target of cybercriminals who have released a malicious clone nearly indistinguishable from the original.
The fake app, distributed through phishing campaigns and deceptive download links, initially allowed attackers to access passwords, personal notes, and wallet details without being able to directly access user funds.
However, within just a year, threat actors have evolved their tactics and are now capable of extracting mnemonic seed phrases, giving them full control of user wallets and enabling them to drain funds.
Evolution of Threats: From Passive Surveillance to Full-Scale Wallet Theft
According to Moonlock’s research, the malware campaign began in August 2024 and has since undergone a rapid and dangerous evolution.
Originally limited to spying on users’ wallet activity, hackers have adapted their strategies to include more aggressive and effective data harvesting.
The latest iterations of the fake Ledger Live app not only mimic the interface of the original software but also deploy deceptive alerts about “suspicious activity” to convince users to enter their 24-word seed phrases.
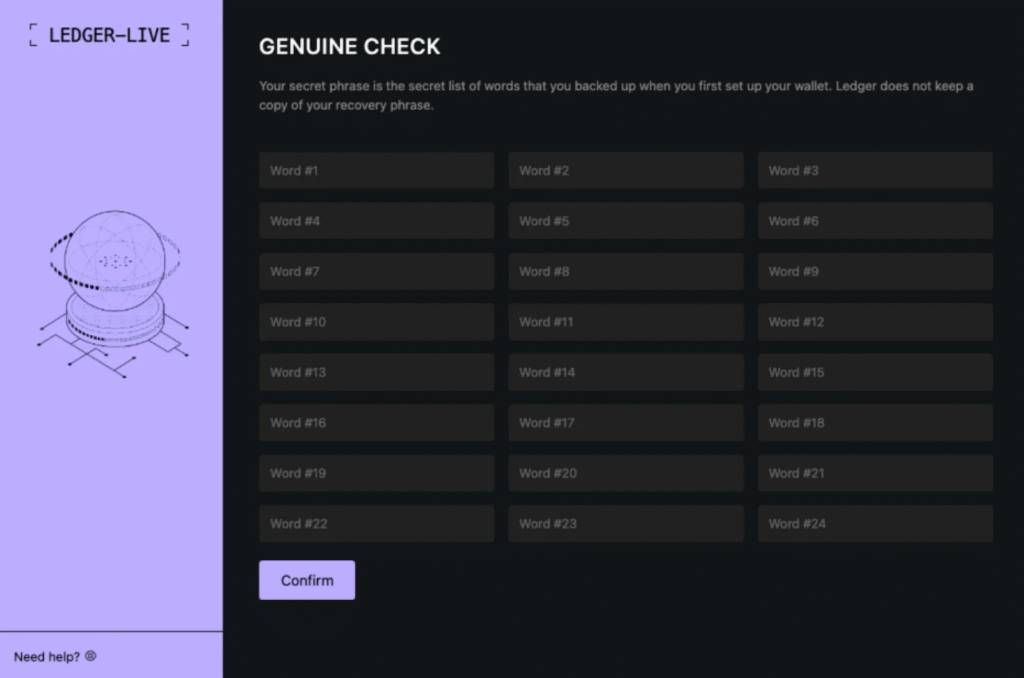
Once entered, these phrases are sent to attacker-controlled servers, giving criminals complete access to users’ wallets and allowing for immediate theft of funds. This shift marks a significant escalation in the threat level facing Ledger Live users.
Also Read: ReversingLabs Uncovers npm-Based Malware Targeting Crypto Users Via Atomic Wallet & Exodus
Key Malware Campaigns and Tactics: AMOS and Odyssey in Focus
Moonlock highlighted four major malware campaigns leveraging these techniques, with particular focus on the Atomic macOS Stealer (AMOS) and a newer, more dangerous variant called Odyssey.
AMOS uses fake installation files to replace the legitimate Ledger Live app, prompting users to disclose sensitive information.
The Odyssey malware, spearheaded by a threat actor named Rodrigo, represents a turning point.
Since March 2025, Odyssey has bypassed multiple security layers by integrating a phishing page that mimics a “critical error” prompt, tricking users into entering their seed phrases.
The phishing component sends both the username and seed phrase to a dedicated command-and-control server, making it extremely difficult for users to detect the breach until it is too late.
The Rise of New Threat Actors and Dark Web Developments
Adding to the complexity of the threat landscape is the emergence of other cybercriminals, such as the actor known as @mentalpositive, who recently advertised a new malware strain with a feature specifically designed to target Ledger Live.
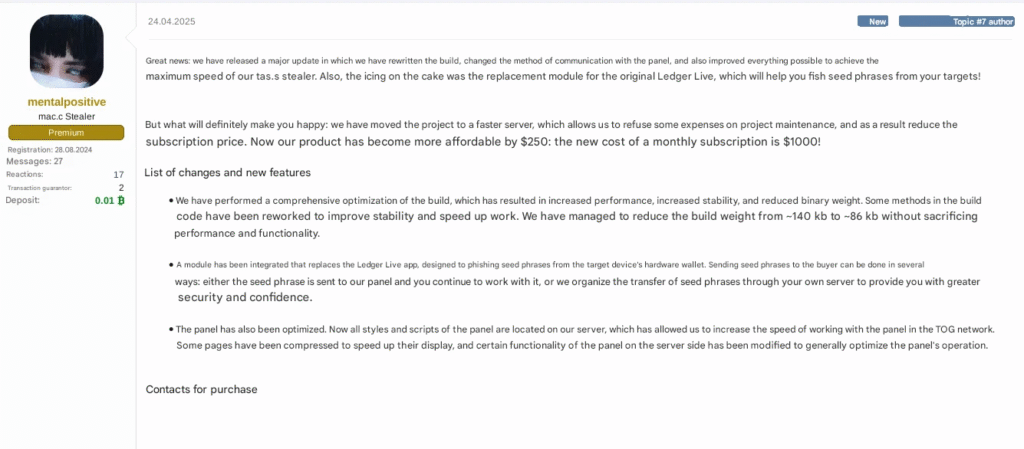
While this malware claims to include a compact “anti-Ledger” module, analysis of recent samples shows limited functional changes, suggesting that the feature may still be under development.
Nevertheless, the samples do include references to Ledger-related directories and demonstrate the capability to exfiltrate browser data, credentials, and crypto wallet files.
Even though the phishing aspect remains inactive, the evolving nature of these tools indicates a high probability of future enhancements that will further endanger crypto holders.
Also Read: South Korea’s SK Telecom Suffers Malware Attack, Bithumb on Alert for USIM Forgery
Stealth and Sophistication: Multi-Stage Attacks Uncovered by Jamf and Moonlock
Further investigation by Jamf Threat Labs and Moonlock uncovered additional campaigns targeting macOS users through seemingly benign Ledger Live installers.
A particularly advanced campaign used a DMG file containing a Mach-O binary packed with PyInstaller to evade detection.
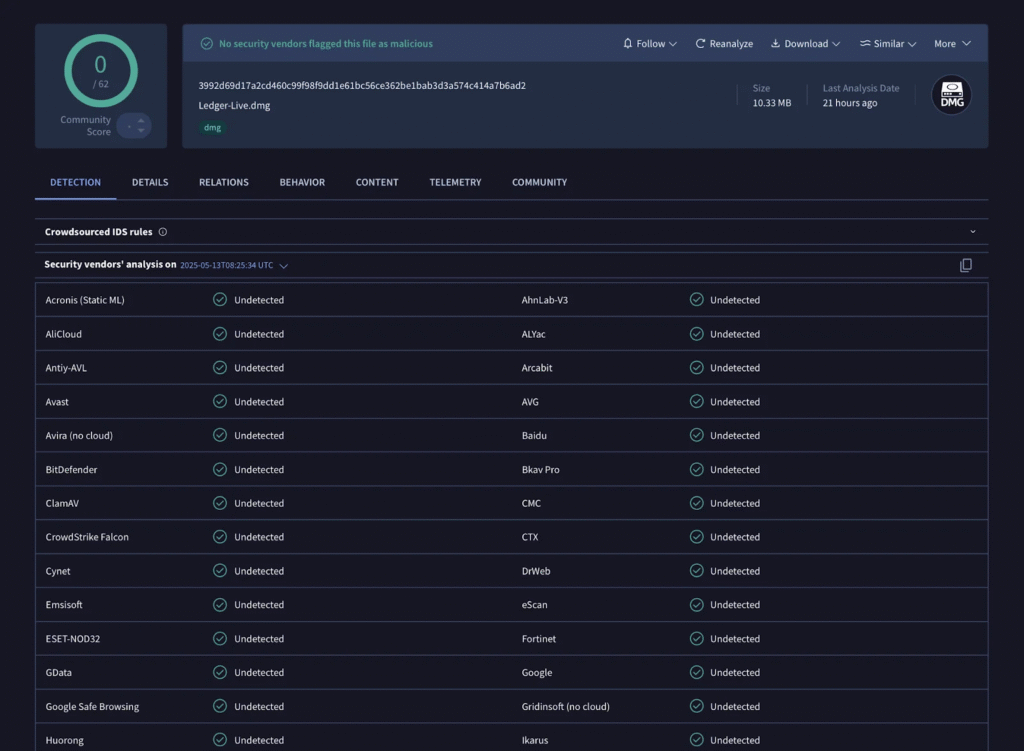
Upon execution, it fetched a phishing page designed to steal credentials through an iframe.
The underlying stealer employed a hybrid approach, combining AppleScript and Python routines to silently gather sensitive information, such as Zoom passwords, Safari cookies, and wallet files, from victims.
The use of multiple programming languages and modular exfiltration methods highlights a new level of sophistication among threat actors, complicating detection and mitigation efforts.
As these attacks grow in stealth and impact, Moonlock urges users to download wallet software only from official sources and to never input seed phrases into apps or websites unless absolutely certain of their legitimacy.
Also Read: Lumma Malware Network Taken Down By Global Forces, Cutting Off Crypto Thefts