
In a recent development earlier today, a new method that hackers are using to evade detection systems by embedding malicious software, code, and links in Ethereum smart contracts was revealed.
ReversingLabs, which specializes in digital asset compliance, indicated that attackers are consistently leveraging code repositories to spread malware in ways that are unlikely to be flagged by security scanners.
ReversingLabs first discovered the malicious activity in open-source packages hosted on the Node Package Manager (NPM) repository, one of the most popular platforms for JavaScript application developers.
This represents a troubling shift in how hackers are violating developer ecosystems.
NPM Packages Used to Hide Malicious Commands
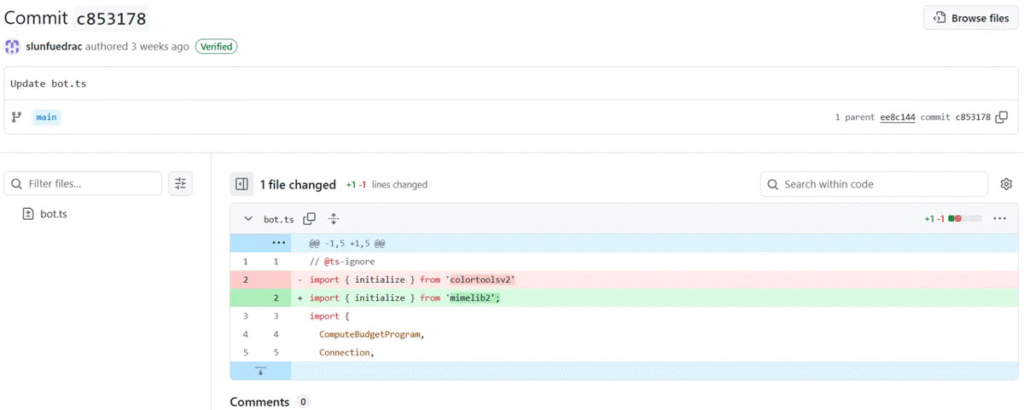
The two identified packages, “colortoolsv2” and “mimelib2”, were published to NPM in July and have been recorded to have malicious activity.
Rather than directly embedding the harmful links in the packages, the hackers used Ethereum smart contracts to hide C2 server addresses.
After installing the packages, the developers run commands that query the Ethereum blockchain. The malicious packages retrieved a URL that would download the second-stage malware payload if the user followed the link and ran the remote commands.
The additional deception led to the benign appearance of harm, as Ethereum blockchain traffic is mixed into regular traffic, and security scans typically do not investigate blockchain traffic patterns.
Also Read: Crypto Hackers Earn $20k Monthly From AI Voice Phishing Scam Targeted At Crypto Executives
A New Evolution in Crypto-Driven Attacks
While malware targeting Ethereum smart contracts isn’t entirely new, using a smart contract to host the URL that would download the second-stage malware is a significant change in operational security.
Earlier this year, there were cyberattacks linked to North Korea’s Lazarus Group that were also blockchain-related.
Regardless, this campaign shows us that cybercriminals are improving their approach by using social engineering techniques to mask their intent and procedures by taking advantage of the decentralized characteristics of a blockchain.
ReversingLabs researcher Lucija Valentić noted that this shows “the rapid evolution of detection evasion techniques” as open-source repositories become attractive targets.
Also Read: Trump Family Backed WLFI Blocks 2 Crypto Hacker Attacks From Compromised End Users, Here’s All
Fake Repositories and Elaborate Social Engineering
The malicious NPM packages were simply part of a larger deception campaign based on social engineering.
Hackers created fake cryptocurrency trading bot repositories on GitHub to entice unsuspecting developers.
The repositories created were convincing enough, with fake commit histories, fake user accounts, fake maintainers, and good documentation to make them look genuine.
The intent was to make the repositories seem legitimate so that developers would download and use them on their own systems, thus continuing the spread of malware.
Also Read: Decentralised Crypto Exchange Bunni Gets Hacked, Hackers Steal $2.4M In Crypto Assets
Growing Threats Across Multiple Blockchains
This incident highlights the significant shift in attacks on open-source repositories in 2024. When the year began, researchers documented a minimum of 23 crypto-related malware campaigns.
The Ethereum exploit is becoming part of an ecosystem of expanding blockchain exploits, which includes a false Solana trading bot on GitHub that propagated malware to steal wallet credentials, and also an attack on “Bitcoinlib,” a library used for development with Bitcoin.
Most recently, Ethereum users were targeted again when the WLFI token holders (backed by members of the Trump family) became victims of a classic EIP-7702 exploit on September 2nd, UnoCrypto reported.
As these events show, there is a growing amount of cyber threats related to crypto and a need for more security inside blockchain ecosystems and open-source communities.
Also Read: Crypto Hack Incidents Lead To $163 Million Losses In August, Marking A 15% Increase From July