
Security firm Koi Security discovered an elite-level cybercrime scheme by a group called “GreedyBear” that pilfered over $1 million in crypto using a complex blend of malicious browser add-ons, tailored malware, and spoofed websites.
According to Koi Security researcher Tuval Admoni, GreedyBear has “redefined industrial-scale crypto theft” as it attacks in several ways simultaneously rather than being specialized in a single modus operandi.
The aggressive diversification is a shift in the techniques of crypto-hunting cybercriminals, away from single-channel scams towards multi-channel and industrial-scale ones.
Over 150 Malicious Extensions Targeting Crypto Wallet Users
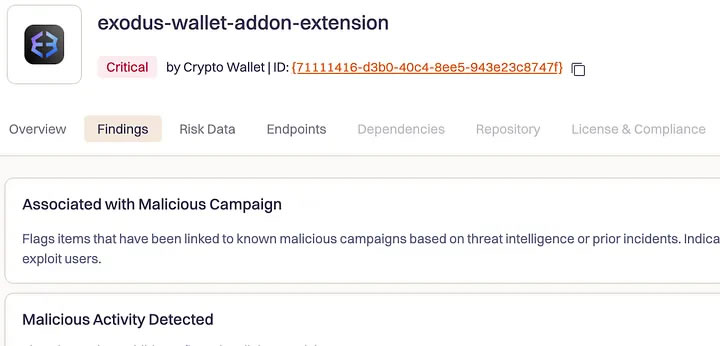
At the center of GreedyBear’s operations is the release of over 150 malicious browser extensions on the Firefox marketplace, designed to mimic well-known crypto wallets such as MetaMask, TronLink, Exodus, and Rabby Wallet.
Via an “Extension Hollowing” technique, hackers upload legitimate extensions first in a bid to bypass security scans in markets before later injecting malware in an attempt to appropriate wallet credentials from fake wallet UIs themselves.
Koi Security’s research linked these extensions to a July “Foxy Wallet” campaign that involved a minimum of 40 malicious Firefox add-ons and is attributed to Russian threat actors
Cryptocurrency investors are warned by security experts like Cyvers’ Deddy Lavid that this exploitation of trust systems is an increasingly serious threat.
Also Read: Crypto Investigator ZachXBT Helps Freeze $5M After Central Bank of Brazil’s $140M Hack
Malware Campaign Spreads Credential Stealers and Ransomware
The following components behind GreedyBear’s big heist involve the distribution of almost 500 samples of crypto-specific malware.
Malware such as LummaStealer harvests wallet information, while ransomware variants such as Luca Stealer ask victims for payment in cryptocurrency.
The majority of this malware is disseminated along Russian-language websites that promote pirated or cracked software, a lure that takes unaware users into clicking on downloaded infected files.
Embedding their malware in all highly demanded illicit downloads keeps a steady trickle of hijacked affairs for GreedyBear, thus paralleling their mass thefts.
Network of Fake Crypto Sites and AI-Driven Scalability
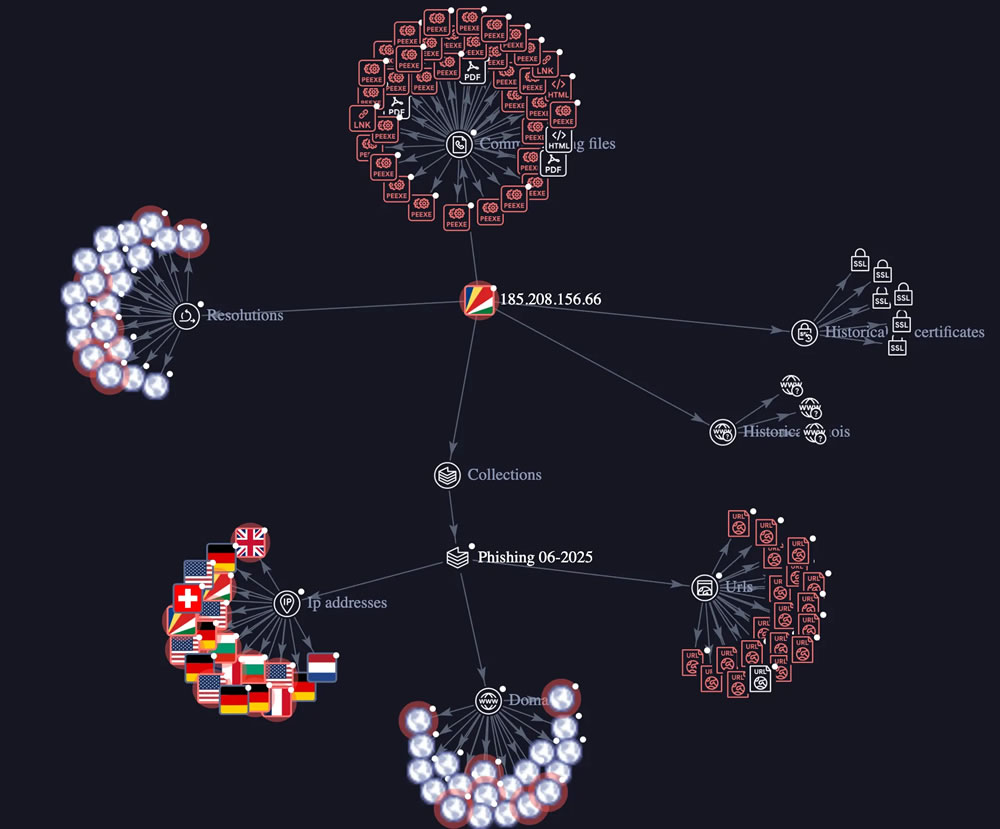
The third pillar of GreedyBear’s operation is a vast network of fake sites posing as replicas of authentic crypto services, including digital wallet products, hardware solutions, and “wallet fixing” software.
Unlike basic phishing sites, the sites are clean and sophisticated, designed to build credibility before stealing confidential data.
All in the attack components are connected to a master command-and-control server that facilitates ransomware distribution, credential scraping, and scam site operations.
Koi Security also discovered evidence of artificially generated code in the campaign, enabling GreedyBear to move rapidly and expand its operations.
Experts warn that this combination of automation, multi-vector attack, and exploiting user trust is a “new normal” of crypto cybercrime, which calls for stricter screening procedures from tech platforms and heightened vigilance from end-users.
Also Read: Crypto Investigators Warn Crypto Users of Fake Aave Site Topping Google Search, Details Inside